The RapidCents Blog
Insights from RapidCents to help you make smarter payment decisions and grow your revenue. Stay updated about news, compliances and more in payment processing solutions with our weekly blog.
Our Latest Blogs
Guides
Insights to Help You Build Smarter Businesses
#guides
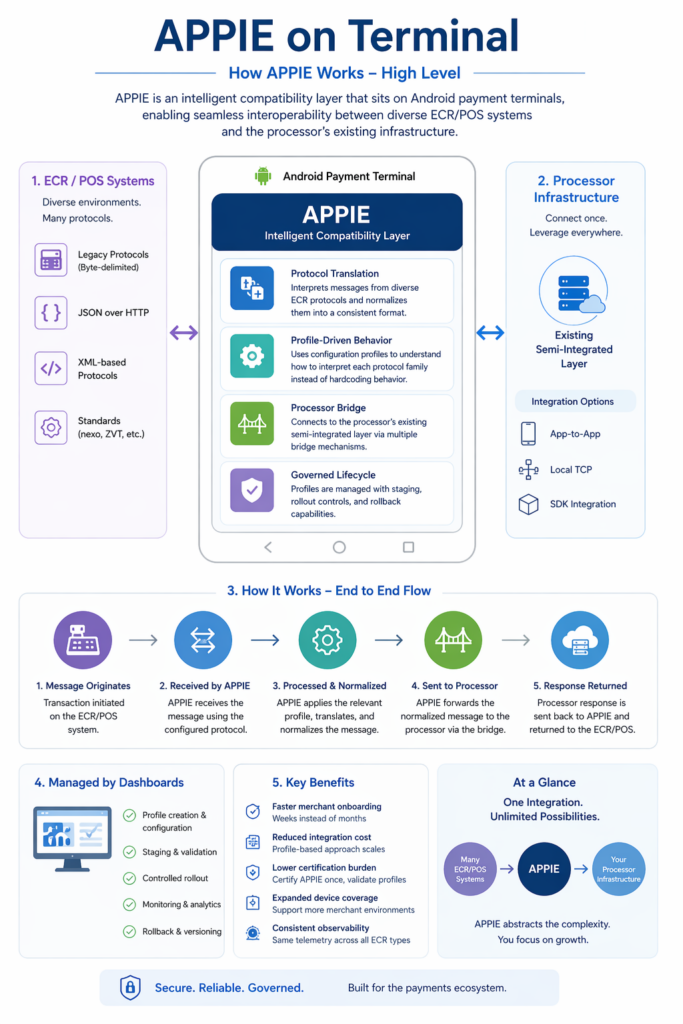
POS Systems for Businesses
Learn how POS systems simplify payments, track sales, and boost efficiency. Explore our complete guide to choosing the right POS.
The Ultimate Guide to Subscriptions and Recurring Billing
A complete 2025 guide to building, managing, and scaling subscription and recurring billing models for modern Canadian businesses.
Virtual Terminal Payments Explained: How to Accept Cards Without a POS System
Learn how virtual terminals work, their benefits, and how to accept secure remote payments from any device with this complete guide.
Blog Categories
Get All Your Payment Solutions On One Platform
Looking for secure, smooth, and scalable payment solutions that are customized for your business? Check out our extensive list of services to help your business increase revenue.
Virtual Terminals
Use any device to accept credit card payments online without any hardware.
POS Terminals
Get paid in-person with on-the counter or mobile point-of-sales terminals.
Recurring Billing
Set up customized subscription plans and process payments at the due date.
Fraud Prevention
Protect the business from chargeback and friendly fraud to maximize revenue.
International Payments
Accept payments from customers all over the globe with scalable solutions.
Payment Links
No-code links and QR codes so you can get paid online instantly.